I’ve been spending a lot of time lately looking at different AI automation setups. Mostly, I’ve just been trying to figure out where the actual leverage is for smaller engineering and ops teams.
What I keep finding? A lot of what we’re calling “AI workflows” are really just traditional, deterministic scripts with a chatbot tacked onto the front.
And for the ones that actually do rely on LLMs for core logic? They end up being surprisingly expensive to run in production. But rarely for the reasons people expect.
📌 The Reality Check
-
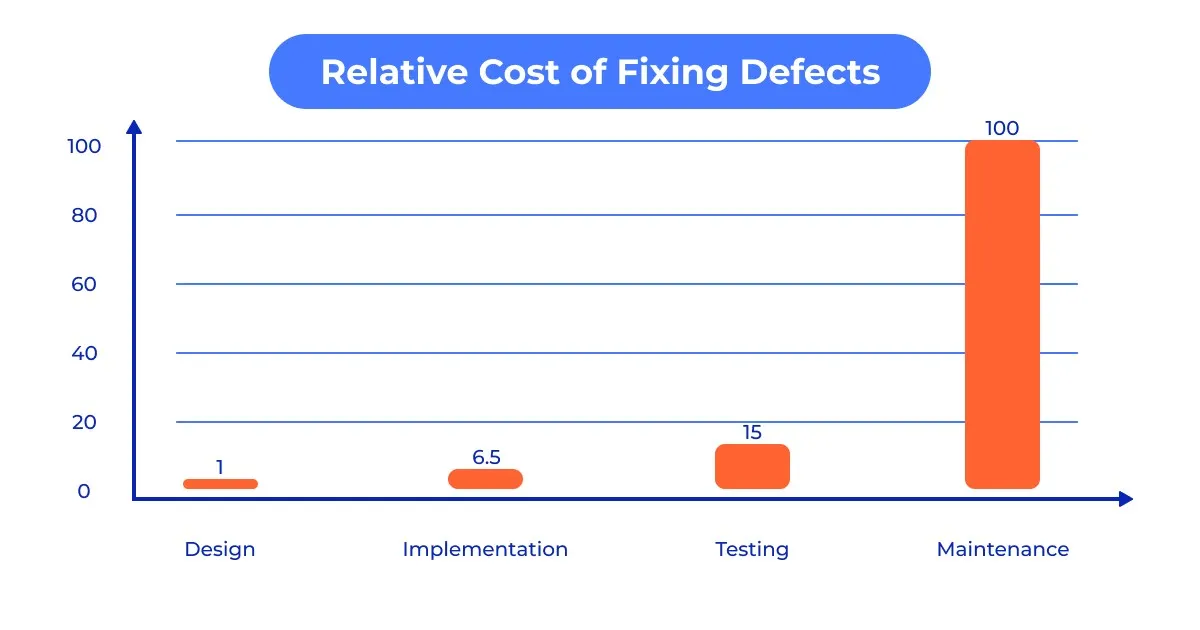
The token bill is a rounding error: You aren’t going broke on OpenAI API calls. You are bleeding cash on the developer time required to figure out why those calls randomly failed over the weekend.
-
Traditional software fails loudly; AI rots silently: An API endpoint changes, and your old code throws a clean 500 Internal Server Error. An AI agent hits an undocumented data format change and confidently writes garbage data into your CRM.
-
Self-hosting is an infrastructure trade-off: Moving to open-source tools like n8n looks cheap on paper right up until you’re debugging Redis queue bottlenecks at 2 AM.
-
Human-in-the-loop often turns into a rubber stamp: When people get alert fatigue from reviewing non-deterministic outputs, they stop auditing and start blindly clicking “approve.”
💸 Why API Token Costs Aren’t the Main Problem
People get really hung up on API token pricing. You see deep comparison guides tracking input/output costs down to the sixth decimal place. And to be fair, inference is remarkably cheap.
But the token bill is almost never what kills a project’s budget.
Just last month, I was working on an automation designed to handle a shared group financial settlement process. The goal was simple: use an LLM to parse detailed bank statement records and automatically reconcile incoming payments and subsidies into a clean tracking sheet for a 10-person group.
The API calls to run the extraction cost pennies. The real cost was the entire weekend spent debugging.
The model kept hallucinating calculated amounts whenever two distinct line items shared an identical transaction date. I ended up spending a massive amount of engineering hours writing fallback scripts, custom schema validators, and data sanitization layers just to handle exceptions for a system that supposedly cost $0.15 to run.
I also realized during all this that I was spending more time trying to fix the prompt than the original manual process would have taken in the first place, which was a slightly depressing moment. Half the time, the workflow technically worked. I just stopped trusting it enough to leave it unattended.
📉 Automation Entropy: How AI Systems Drift Over Time

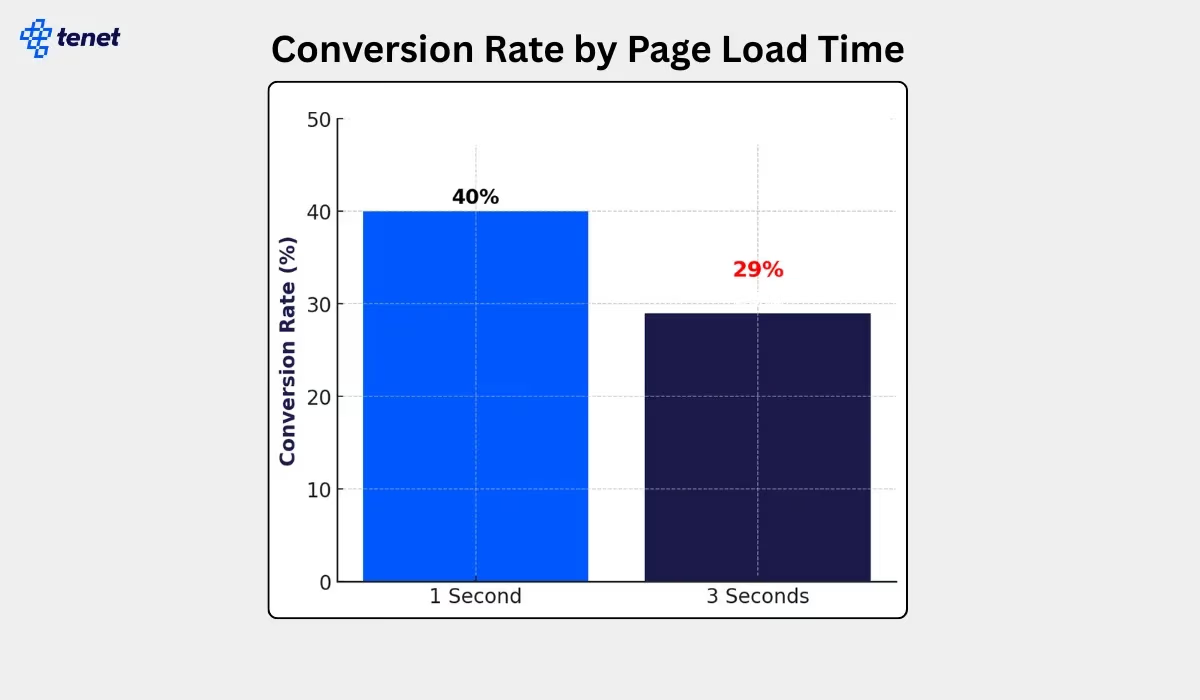
When you test an AI pipeline in a closed environment, it feels like magic. But production environments are fundamentally unsympathetic to probabilistic software.
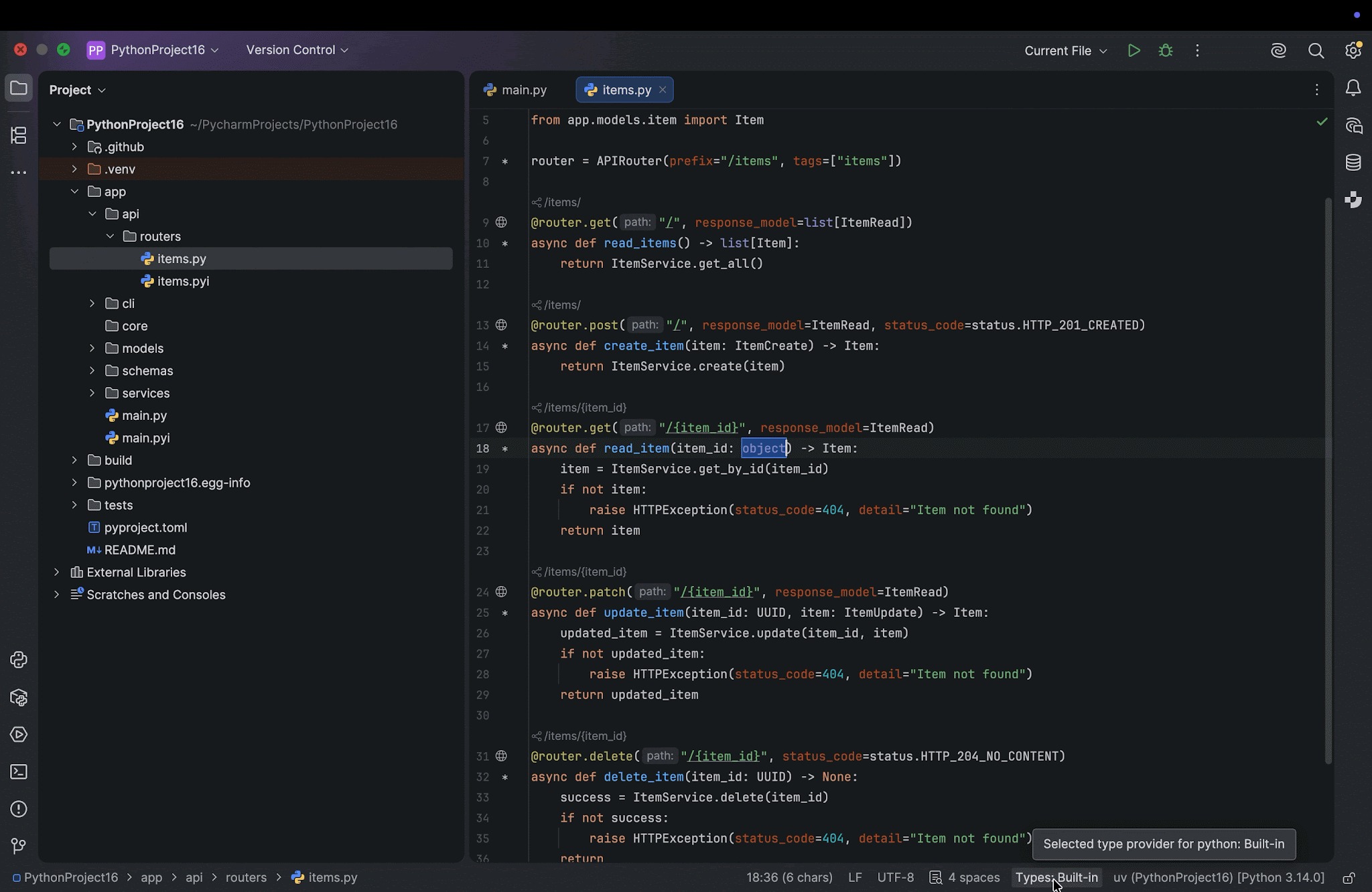
Traditional software infrastructure is rigid, which makes it stable. You write a Python script that pulls a specific JSON key from a third-party API. It runs cleanly until the third party deprecates the endpoint. When it breaks, it throws a loud exception.
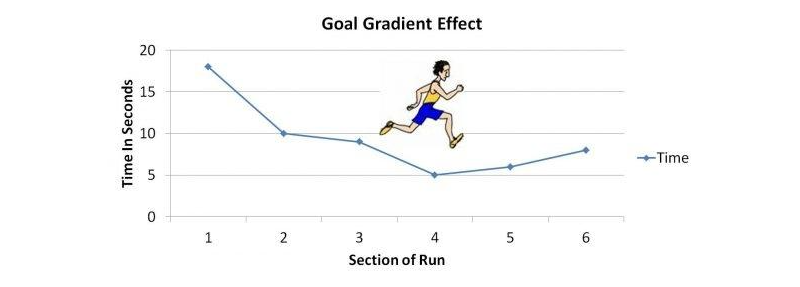
AI systems are vulnerable to a much subtler decay: Automation Entropy. The models change. The data changes. Eventually the workflow starts drifting. If you look closely at how AI agents vs traditional automation interact, you’ll see a massive divergence in long-term reliability.
A few months ago, I was helping a 6-member team build out a specialized chatbot designed to estimate groundwater variations by reading through highly unstructured geological reports. In the dev sandbox, our vector retrieval setup was crushing every test query.
Then we pushed it live and left it unattended over a weekend.
An upstream source changed its document formatting slightly, and our pipeline experienced a sudden timeout loop that nobody had properly caught in the error-handling config. The retry queues backed up silently. Because the system aggressively retried failed steps without a hard circuit breaker, it repeatedly hammered the model endpoints. By Monday morning, we didn’t have an elegant groundwater report—we had a backed-up queue, duplicated database writes, and an incredibly messy cleanup job.
At some point, somebody still ends up babysitting the thing. Maybe less than before, sure, but definitely not zero. This is a core part of ai reliability engineering that most teams ignore until their production data gets corrupted.
You can usually tell an AI pipeline is succumbing to operational rot when nobody on the engineering team wants to touch the prompt anymore. The instruction set becomes an accumulation of hyper-specific edge cases like: “Do not format dates as DD/MM if the client is based in North America, unless the text explicitly references European logistics hubs, and make sure to ignore headers that look like…”
We’ve moved past basic text prompt generation at this stage; what you are actually dealing with is what context engineering is and why prompt engineering is no longer enough. Without it, the prompt becomes just as fragile as legacy regex code.
🏗️ Self-Hosting vs. SaaS: The Infrastructure Trapdoor
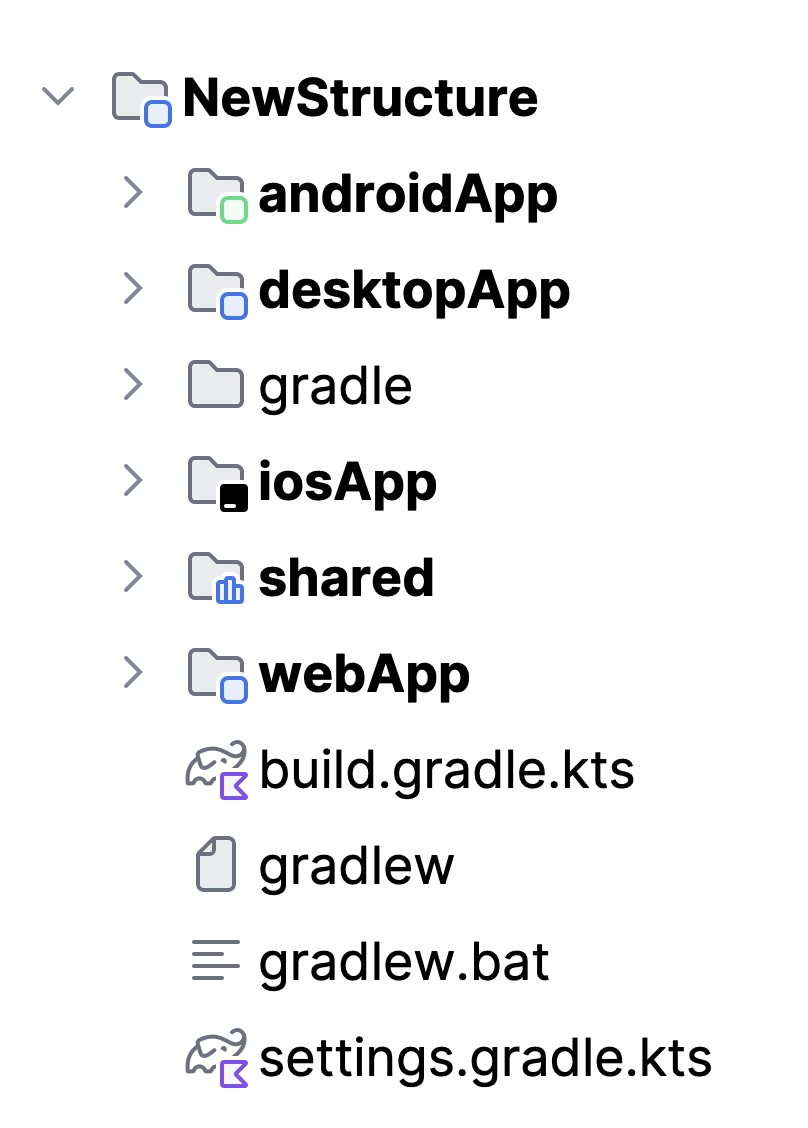
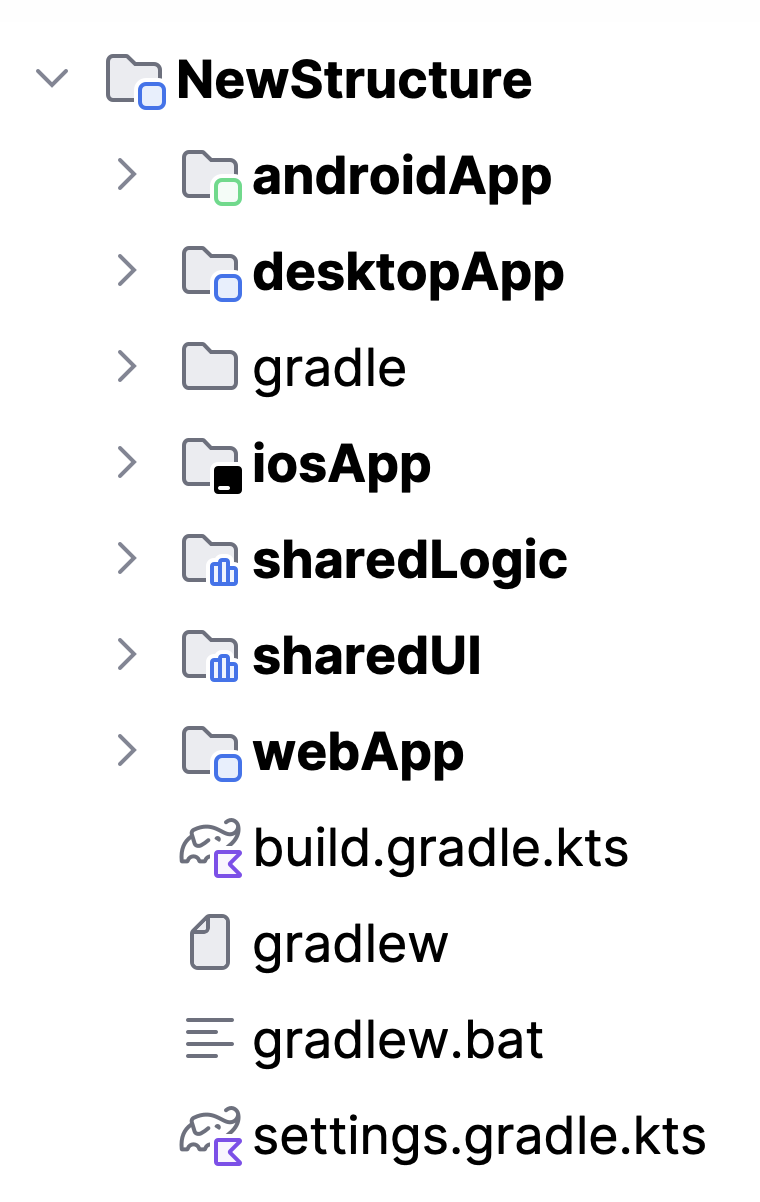
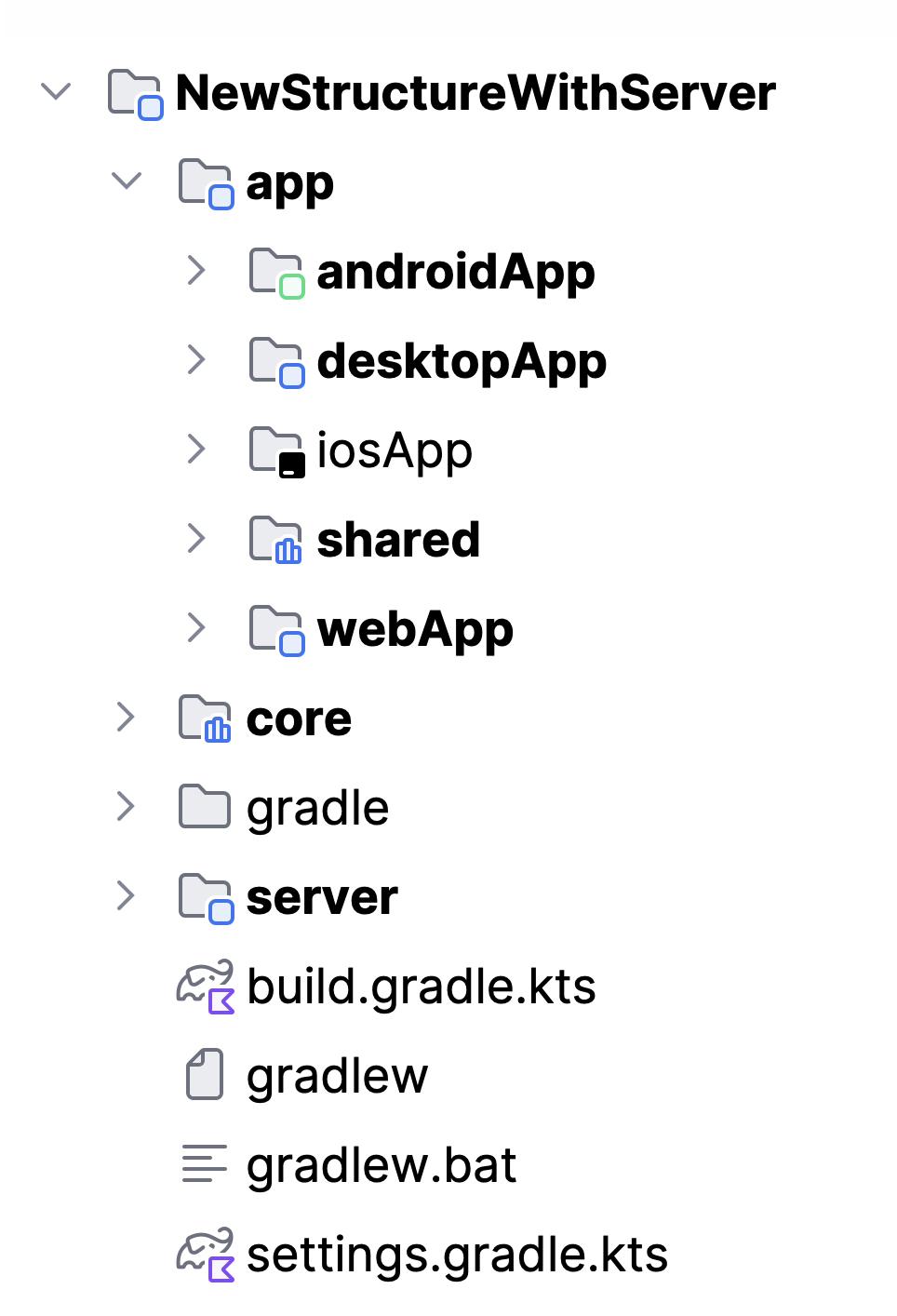
When the monthly usage bills from managed platforms start scaling up, teams face a choice: stay on a managed platform or spin up an open-source framework.
At first glance, understanding what is n8n and why companies are replacing zapier with open automation looks like an open-and-shut financial win. You replace unpredictable execution tiers with a predictable monthly server invoice.
At first, self-hosting honestly feels great. The dashboard looks clean, everything is fast, and you stop thinking about usage-based pricing for a while. I remember feeling weirdly proud the first time I had n8n running properly on a tiny AWS instance.
Then a few weeks later something broke at 1 AM and suddenly I was reading Redis documentation instead of sleeping.
We’d had a spike in webhook traffic, the node ran out of memory, and because I hadn’t configured a durable queue, we lost a bunch of active state data. You realize pretty quickly that when you self-host, you’re not just saving on software fees. You are essentially volunteering for a DevOps role to patch server vulnerabilities and manage uptime alerts. For some teams, that makes sense. For me, it was exhausting.
The Three Big Choices:
-
Managed iPaaS (zapier vs make vs n8n): Best for rapid prototyping and isolated tasks. The catch is that per-execution billing scales aggressively, and visual logic becomes unmanageable spaghetti past 20 nodes. Low scalability ceiling.
-
Self-Hosted Tools: Best for high-volume pipelines managed by technical teams who are willing to run their own infrastructure. If you look at the 8 best ai workflow automation tools in 2026, self-hosting can save money at high scale, but you pay for it in maintenance overhead.
-
Code-First Frameworks (what is langchain and langgraph): Best for multi-stage reasoning agents and core product features. If you are learning how to build a rag system with pgvector and langchain, code gives you absolute control over state machines and fallback logic.
🛑 Why “Human-in-the-Loop” Often Breaks Down
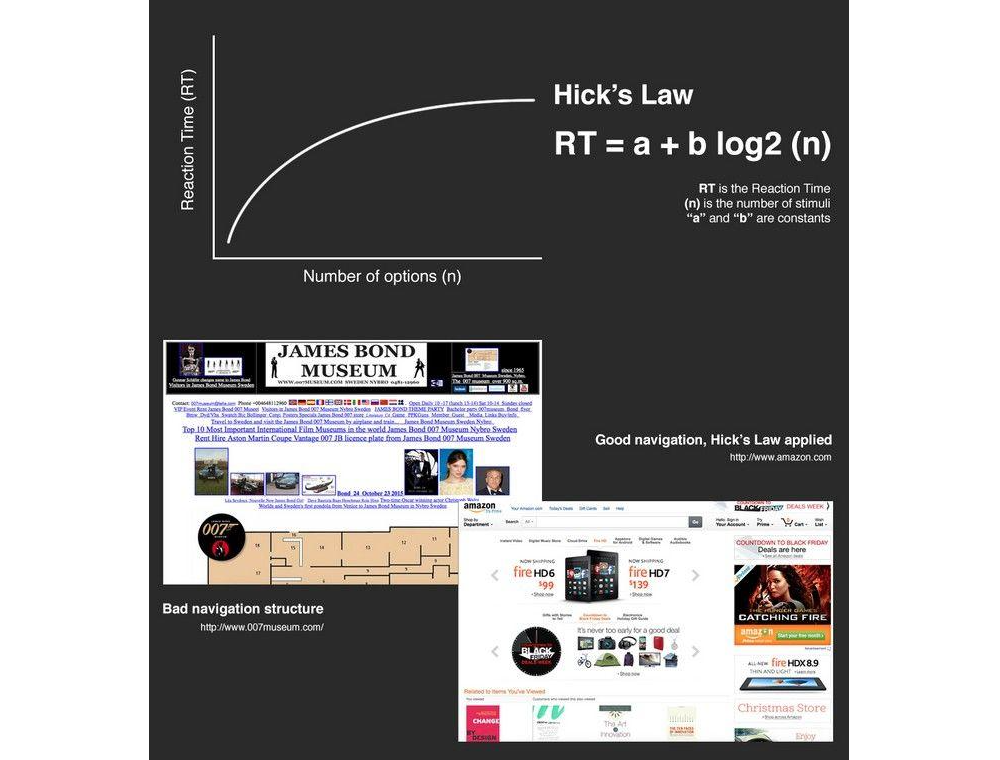
When a workflow requires high accuracy, the instinctive response is to introduce a human approval stage. The AI handles the messy work and stages the output as a draft. A human operator reads it and clicks “execute.”
In theory, this gives you the efficiency of automation with the safety net of human judgment. In practice, it frequently creates Alert Fatigue.
The pattern loops like this: High Output Volume leads to Repetitive Safe Approvals, which causes Attention Drops, resulting in the Blind Approval of Garbage.
By week three of operating the pipeline, operators are no longer reading the text critically. They are simply click-approving hundreds of staged payloads a day to clear their queue. The human presence stops being an active safety filter and becomes a passive rubber stamp. You haven’t bought meaningful leverage; you’ve just assigned an employee a massive, daily proofreading chore. If you look at how companies try to solve this when figuring out how to build an ai agent for your business, managing human override fatigue is always the hardest piece of user experience to design.
💻 Stop Making Everything an Agent
The industry currently has an obsession with making everything agentic.
If the logic of your business process can be mapped out using clear, conditional rules (if X data is present, route to Y database), you should not be using an AI agent. Deterministic code is infinitely scalable, lightning fast, and entirely predictable. Look for real automations that save time using simple scripts before forcing an LLM to guess the next step.
Save agentic frameworks for highly unstructured problems—like interpreting natural human sentiment or normalizing chaotic, multi-source text summaries. If you’re building out production ai systems, it’s worth reading up on what is mcp model context protocol ai agents to see how models should clean up their tool interactions instead of relying on open-ended logic loops.
🛠️ The Real Engineering
AI automations simply do not behave like standard software licenses. They behave far more like human operational hires. They are flexible, capable of handling incredible complexity, and occasionally brilliant—but they require ongoing management, structural constraints, and deliberate oversight to keep them from wandering off course.
The API call is always the cheapest part of your architecture. Managing the unpredictability that surrounds it is where the real engineering begins.